A recent cybersecurity discovery unveils a sophisticated cryptojacking campaign utilizing vulnerable drivers to neutralize established security solutions, notably EDRs, in what’s known as a Bring Your Own Vulnerable Driver (BYOVD) attack.
Elastic Security Labs is actively monitoring this campaign, identified as REF4578, with its primary payload named GHOSTENGINE. Previous findings by Chinese cybersecurity firm Antiy Labs dubbed this operation HIDDEN SHOVEL.
According to Elastic researchers Salim Bitam, Samir Bousseaden, Terrance DeJesus, and Andrew Pease, GHOSTENGINE exploits vulnerable drivers to terminate and remove EDR agents, ensuring smooth operation of the deployed coin miner. This campaign demonstrates an unusual level of complexity aimed at both installing and persisting the XMRig miner.
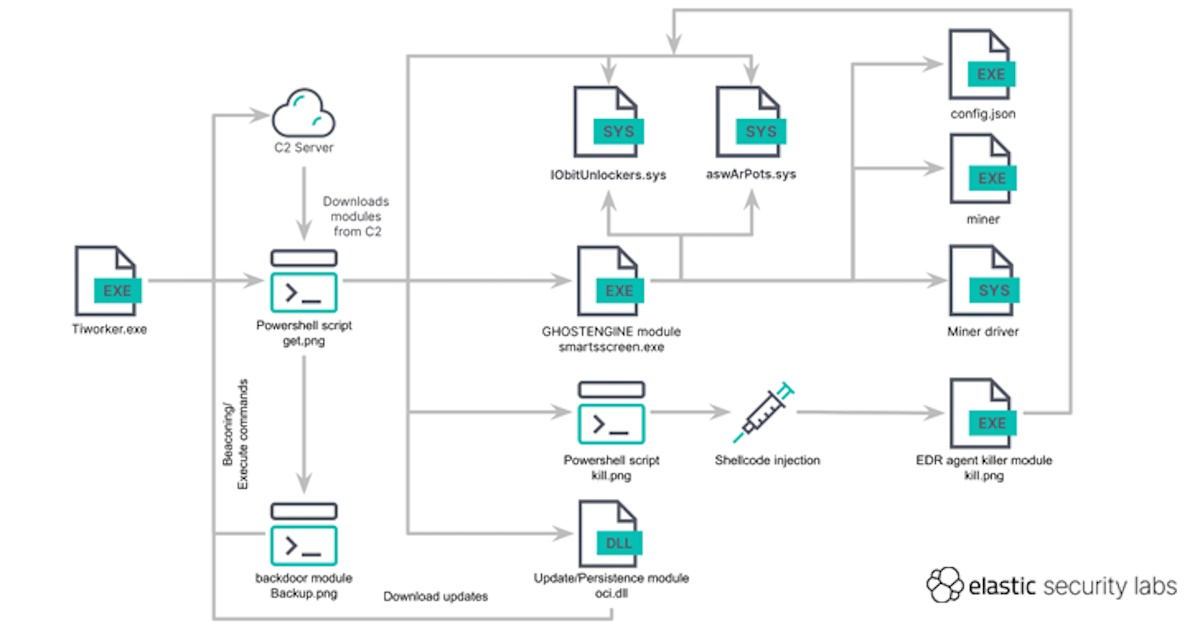
The operation kicks off with the execution of “Tiworker.exe,” triggering a PowerShell script to fetch additional payloads from a command-and-control (C2) server disguised as a PNG image (“get.png”). These modules, including “aswArPot.sys,” “IObitUnlockers.sys,” “curl.exe,” “smartsscreen.exe,” “oci.dll,” “backup.png,” and “kill.png,” are then deployed on the infected host via HTTP, with an FTP-based fallback mechanism in place.
Furthermore, the malware attempts to disable Microsoft Defender Antivirus, clear event log channels, and ensure sufficient storage space for file downloads, which are stashed in the C:\Windows\Fonts folder.
The PowerShell script creates scheduled tasks to run malicious processes periodically, ensuring the persistence and execution of the core payload, “smartsscreen.exe” (GHOSTENGINE).
GHOSTENGINE deactivates security processes using the vulnerable Avast driver (“aswArPot.sys”), deletes security agent binaries, and executes the XMRig miner. Subsequently, another vulnerable driver from IObit (“iobitunlockers.sys”) deletes the security agent binary, followed by the execution of the XMRig client mining program.
To ensure persistence and updates, a DLL file fetches the get.png script and executes it, while the “backup.png” PowerShell script functions as a backdoor for remote command execution. The PowerShell script “kill.png” serves as a redundancy measure, capable of deleting security agent binaries by injecting and loading an executable file into memory.
This discovery coincides with the Uptycs Threat Research Team’s findings of a large-scale operation exploiting Log4j vulnerabilities to deliver an XMRig miner since January 2024.
BYOVD represents a growing threat tactic, leveraging vulnerable drivers to undermine security mechanisms and operate stealthily at the kernel level. Although Microsoft has deployed the Vulnerable Driver Blocklist, manual updates are necessary for optimal protection.
While the full scope of the campaign and its perpetrators remains unknown, the sophistication displayed in this apparent cryptojacking attack warrants attention within the cybersecurity community. This disclosure also follows recent discoveries of novel techniques like EDRaser, targeting Microsoft Defender flaws, and bypass methods against security solutions, underscoring the ongoing arms race between threat actors and cybersecurity defenders.
Source: thehackernews.com












Got a Questions?
Find us on Socials or Contact us and we’ll get back to you as soon as possible.